|
Cyber Predator is an Internet/Network
security and activity monitor
 In Real-Time it
sniffs all internet/intranet/extranet traffic to and from the
clients browser looking for
key (naughty) words in the content,
and in real time will alert a manager/administrator of the
naughty activity. In Real-Time it
sniffs all internet/intranet/extranet traffic to and from the
clients browser looking for
key (naughty) words in the content,
and in real time will alert a manager/administrator of the
naughty activity.
It also logs
browser activity, so you can see what your traffic patterns are,
who visited what site and when, this product not only identifies
the client IP address, but (if they are using Microsoft Windows™
and Microsoft Networking), it will tell you the PC Name, and the
user logged onto that PC at the time, Logon name and Full Name.
 It has several pages of treeviews (Like
Explorer) so you can drill down into Users to see what sites
they visited what pages they viewed and how long for. You can look at sites, and see what users
visited them, and you can look at PC's to see what sites they
have visited and what pages they viewed. You also can see the
violation words and associated users.
It has several pages of treeviews (Like
Explorer) so you can drill down into Users to see what sites
they visited what pages they viewed and how long for. You can look at sites, and see what users
visited them, and you can look at PC's to see what sites they
have visited and what pages they viewed. You also can see the
violation words and associated users.
Features
| Does it
tell me how long each user was looking at each
page/site |
Yes |
| Does it
tell me the users Logon Name, Full Name, PC Name
as well as the PCs IP Address |
Yes |
| Will it
alert me in real-time when some naughty activity
is happening |
Yes |
| Can I
look back at users activity, naughty or good ? |
Yes |
| Can I
see activity graphs |
Yes
several |
| How long
does it take to install |
Less
than 15 minutes |
| Does it
need updating all the time with web site
addresses |
No |
| Does it
require a proxy server or any other similar item |
No |
| Do we
have to install anything at all on the users
PC's |
No |
| Do the
users know they are being monitored |
Only if
you tell them |
| Can the
users bypass or uninstall the software |
No, its
not installed on the users PC |
| Does it
only get naughty words in the web site name |
No, all
the activity is scanned |
| Will it
slow my network down |
No, it
is a listening system not a pass thru |
|
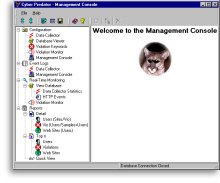
What
do the screens look like ?
Why
is Cyber Predator so good ?
Most security and monitor tools around at
the moment, get their information from proxy server log files,
and whilst the products themselves may be very good, this method
of working has several failings:-
- Proxy servers normally only provide the
users logon ID (in a Microsoft environment Cyber
Predator will give you the users FullName, ideal for
colleges/universities where users have non obvious logon
IDs)
- It will tell you how many seconds each
page was viewed by each user.
- The information is historical (Cyber
Predator works in Real-Time)
- Proxy servers cost money (Cyber
Predator doesn't need a proxy server to work.
- Proxy servers log the URL's that people
type into the address box in their browsers, if this doesn't
contain naughty words then the trick is missed (Cyber
Predator actually sniffs all the data on the network, to
and from the browser, thereby allowing it to pick up any
occurrence of a naughty word in any part of the data, not
just the URL).
- Proxy Servers only log traffic going
through them, which in the main does not include Intranet
traffic. (Cyber Predator monitors all browser traffic on
your network).
- There is NO client software to install
on any PC, just install Cyber Predator onto an NT4+
platform and that's it.
Some other security tools actually block
sites so the user can't see them at all, a good idea, but:-
- Most of them block the whole site, so
the 99% of useful information on that site is also blocked
- Most of them require continuous
updating, adding URLs of naughty sites, this takes time, you can buy into an updating service, but that costs
money.
- They sit in the data stream, slowing it
down (Cyber Predator listens unobtrusively to the data,
therefore does not slow it down).
Cyber Predator, is a Zero Admin, one time
purchase, Real-Time activity monitoring system which will alert
you of the naughty content of a site before its even displayed
on your users screen !,
What
will it do for you ?
It gives you Peace of mind, if you're
Violation Console isn't making noises then you know people
aren't visiting the sites containing naughty words.
It also protects you from the legal point
of view too:-
- Visitors to a lot of web sites are
monitored, this at the very least exposes you to that web
site, what happens to that information ?, it wouldn't be
very nice to see that employees from your company for
example are the most frequent visitors to a naughty web
site.
- Harassment, imagine the cost and hassle
of court proceedings, because one employee has something
displayed on their PC that offends another employee.
- Increase your companies bottom line, at
the end of the day, companies employ people to work, and
ultimately they contribute to the profit of the company, if
they are not working, they are losing you money !, not only
one person either, when people find something interesting on
the web, they quite often tell their friends who visit the site as well.
- Increase your bandwidth,
you pay for your connection to the internet,
this extra non business traffic is costing you real
money because it is slowing down the link for the rest of the
users.
- Increase your companies bottom line, if
a user spends only 10 minutes a day, looking at non business
related material on the web, this has cost you the
equivalent of more than a weeks salary (based on 220 working
days per year and a 36 hour working week), but the really
bad thing is if they tell 3 friends, you could be losing a
month per year of man power per 4 people.
- Some magazines quote 90 minutes per day
of non-business surfing !! that's 9 weeks per year per user.
Why
do you need it ?
Maybe you don't, but how do you know they aren't
abusing this resource if you don't keep an eye on it ?
What
dependencies does it have ?
- The main monitor program runs as a
service on a machine running any 32 or 64 bit version of Microsoft Windows with min 512MB Ram and 2GB of free disk, Ethernet card that supports
promiscuous mode (Most Ethernet cards do).
- An Ethernet network (LAN) that connects
all your PC's together.
- Some users to monitor.
What
programs do I get with Cyber Predator ?
The Cyber Predator suite consists of:-
- The Real-Time Data Collector, runs on
any 32 or 64 bit version of Microsoft Windows, this sniffs the network and provides monitoring and logging
functions.
- The Management
Console a fully integrated control centre, it deals with
configuration, reports, and all the Real-time monitoring
capabilities, it includes a built in Real-Time
Violation Monitor, which collects the messages generated
by the Real-Time Data Collector, this is normally run on an
administrator or managers PC.
- The Setup Program, this is where the
initial Data Collector configuration is done, the fine
tuning is done in the Management
Console.
All these applications can be run on the
same machine, as would probably be the case for a small network,
or each one can run on a different machine, as would probably be
the case in larger networks.
Is
it easy to configure ?
Yes, all configuration is done from the
users workstation, answer a few questions, tune the keyword
list, then monitor.
The keyword list can contain any words you
wish, e.g. Football, Soccer, any browser activity containing these
words would be reported. You can modify this
list whenever you wish.
How
much does it cost ?
Visit our Online
Store to calculate the total cost for your number of PCs.
Download
the Free 30 day Trial
|